Spam labels, blocked calls, and falling answer rates can damage outbound operations long before anyone says the word “compliance.” That is why this stir shaken compliance guide matters now. The market often treats STIR/SHAKEN as either a simple checkbox or a fully outsourced vendor problem, and both views are incomplete.
This plain-English compliance reference explains what STIR/SHAKEN actually means, who is responsible, what changed under recent FCC guidance, which risks matter most, and what your team should review now before trust and call performance deteriorate further.
What STIR/SHAKEN Compliance Means in Plain English
STIR/SHAKEN compliance is a caller ID authentication framework used to help confirm that a call is really coming from the party it claims to come from. In practical terms, it is designed to reduce spoofed caller IDs and support more trustworthy voice traffic across IP-based calling networks. In the FCC context, it is part of a broader push to improve call authentication and reduce harmful robocall activity.
For business users, the simplest mental model is this: a provider signs the call, the network passes that identity information along, and the receiving side checks whether the calling identity can be trusted. That process relies on digital certificates, which act like trust credentials in the calling chain. You do not need to understand telecom protocol internals to understand the business takeaway: authenticated identity supports stronger caller trust than unauthenticated traffic.

Why this matters in real operations:
- Lower trust can contribute to spam labeling and weaker answer rates.
- Outbound teams often notice the issue through campaign performance before a formal review begins.
- Caller ID verification can support reputation, but it is only one part of the calling trust equation.
- Businesses using VoIP and outbound campaigns still need visibility into how their calls are authenticated.
Important: STIR/SHAKEN helps authenticate caller identity. It does not replace broader telemarketing or consent compliance.
What “STIR” and “SHAKEN” Stand For
- STIR = Secure Telephone Identity Revisited
- SHAKEN = Signature-based Handling of Asserted information using toKENs
The acronyms matter less than the practical function: verifying caller identity in a way that supports more trustworthy call handling.
What Attestation Means, and What It Does Not Mean
Attestation levels describe a provider’s level of confidence in the calling party and that party’s right to use a number. In plain English, attestation is a trust statement attached to the call authentication process, not a blanket statement that every call is lawful in every sense.
Higher attestation can support stronger trust signals, but it is not the same as marketing consent, lawful outreach approval, or universal call acceptance. It mainly supports caller ID spoofing prevention and authenticated identity handling.
Clarification: Attestation helps show confidence in number use and call origin. It does not automatically mean the call meets every legal or policy requirement beyond STIR/SHAKEN.
Who Needs to Care About STIR/SHAKEN Compliance
The short answer is: Voice Service Providers often carry the direct responsibility in many FCC-related compliance contexts, but businesses that rely on outbound calling still face meaningful operational and governance exposure. This is not only a carrier issue.
Teams that should pay close attention include:
- Voice Service Providers (VSPs): Often directly responsible for meeting relevant robocall mitigation standards and call authentication obligations.
- Businesses using outbound calling: Exposed through answer-rate declines, spam tags, blocked traffic, and poor vendor visibility.
- BPOs and contact center operators: Especially vulnerable when large campaign volumes depend on stable trust and clear escalation paths.
- Resellers and intermediaries: Often sit in setups where responsibility is split across multiple parties.
- Ops, IT, and telecom teams: Need to understand how VoIP providers and routing relationships affect performance and accountability.
- Companies using cloud-based calling stacks: Cloud call center infrastructure does not remove the need for verification.

A common blind spot is assuming, “My provider handles everything.” In many cases, the provider may own core implementation duties, but the business still owns vendor review, number governance, escalation readiness, and internal visibility. If your team does not know who signs your calls, who sets attestation, or how issues are investigated, your risk is not just regulatory. It is operational.
The practical rule is simple: even if you are not the directly regulated party, you should still verify how your calling environment is set up.
Direct Responsibility vs Indirect Responsibility
| Type | What It Usually Means |
|---|---|
| Provider responsibility | Providers often own direct compliance duties related to implementation, authentication, and filing obligations where applicable. |
| Vendor governance | Businesses own vendor review, internal controls, campaign oversight, and verification of who does what. |
Both sides need accountability. One party may own the formal requirement, but both can feel the impact when trust breaks down.
Why Businesses Still Need to Verify Their Provider Setup
Provider claims alone are not enough. Businesses should understand routing transparency, confirm number ownership, know who signs outbound calls, and know who investigates sudden spam tags or answer-rate drops. In practice, the biggest issue for many teams is not direct FCC filing responsibility. It is weak visibility into the calling chain and unclear escalation when performance changes fast.
The Latest FCC Changes Businesses and Providers Should Know
Recent FCC changes matter because they shift more accountability back to the provider that is actually responsible for originating or handling calls. For operations teams, the impact is practical: less room for vague ownership, more emphasis on traceable authentication decisions, and greater exposure if compliance protocols are outdated. This section is a business summary, not legal advice, and readers should verify current obligations against official FCC guidance.
What changed / Why it matters
-
The FCC Eighth Report and Order raised accountability expectations.
Providers need a clearer, more direct role in call authentication rather than relying on loose third-party arrangements. -
Provider-owned certificates became a key compliance requirement.
In relevant scenarios, providers are expected to sign calls using certificates they own, not simply depend on another party’s certificate. -
Providers must make their own attestation decisions.
Attestation is no longer something that should be treated as a blind outsourced function. -
The Robocall Mitigation Database matters more to compliance posture.
Database status and mitigation-plan accuracy are tied to how providers represent and maintain their authentication approach. -
Rule evolution is continuing into 2026.
Teams should monitor FCC updates rather than assume the framework is settled forever.
These changes are important because they target a real market weakness: unclear responsibility in the trust chain. In practice, over-attestation, vague upstream dependencies, and outsourced decision-making have made it harder to separate legitimate traffic from bad traffic. That creates both compliance risk and call trust problems.
For businesses, the biggest takeaway is not that every company suddenly has a new filing duty. It is that your provider’s compliance posture now has more direct consequences for your outbound operations. If a provider cannot explain ownership, attestation logic, or database status in plain English, that is a governance issue.
There is also a broader industry context. STIR/SHAKEN has helped improve call authentication, but it has not solved all robocall or trust issues. Industry reporting has continued to highlight uneven implementation, smaller-provider challenges, and signs of over-attestation in some traffic environments. That is why businesses should view FCC call authentication rules as part of a larger trust and governance framework, not as a standalone cure-all.
Provider-Owned Certificate Requirement
- Provider-owned certificates mean the provider should use a certificate tied to its own authority and identity when performing call signing in relevant compliance situations.
- This reduces the risk of accountability being blurred across third parties that do not truly own the calling relationship.
- If a third party supports the technical process, the provider still needs to retain ownership and responsibility.
- At a business level, certificate ownership matters because it makes escalation and accountability clearer.
Providers Must Make Their Own Attestation Decisions
Recent guidance reinforces that providers should make their own attestation decisions rather than treat attestation like an outsourced checkbox. That matters because blind delegation can increase the risk of over-attestation, where traffic receives stronger trust signals than it should. In business terms, this is about accountability in the trust chain. A provider should be able to explain why a call received a certain attestation level and what information supports that decision.
2026 Watchlist, What Teams Should Monitor Next
- KYUP refinement: The FCC has signaled interest in stronger Know-Your-Upstream-Provider expectations to improve upstream accountability.
- Higher attestation scrutiny: Watch for tougher expectations around how providers justify attestation assignments.
- International call labeling: Foreign-originated traffic and offshore use of U.S. numbers may face tighter review and labeling rules.
- Rich Call Data: Verified names, logos, or contextual caller information may become more relevant, but support remains uneven.
- State-level activity: Some states are exploring their own authentication-related measures, which could add complexity.
These are evolving topics, not all final obligations. Teams should monitor official FCC updates and provider communications closely.
STIR/SHAKEN Compliance Risks: What Happens if Things Go Wrong
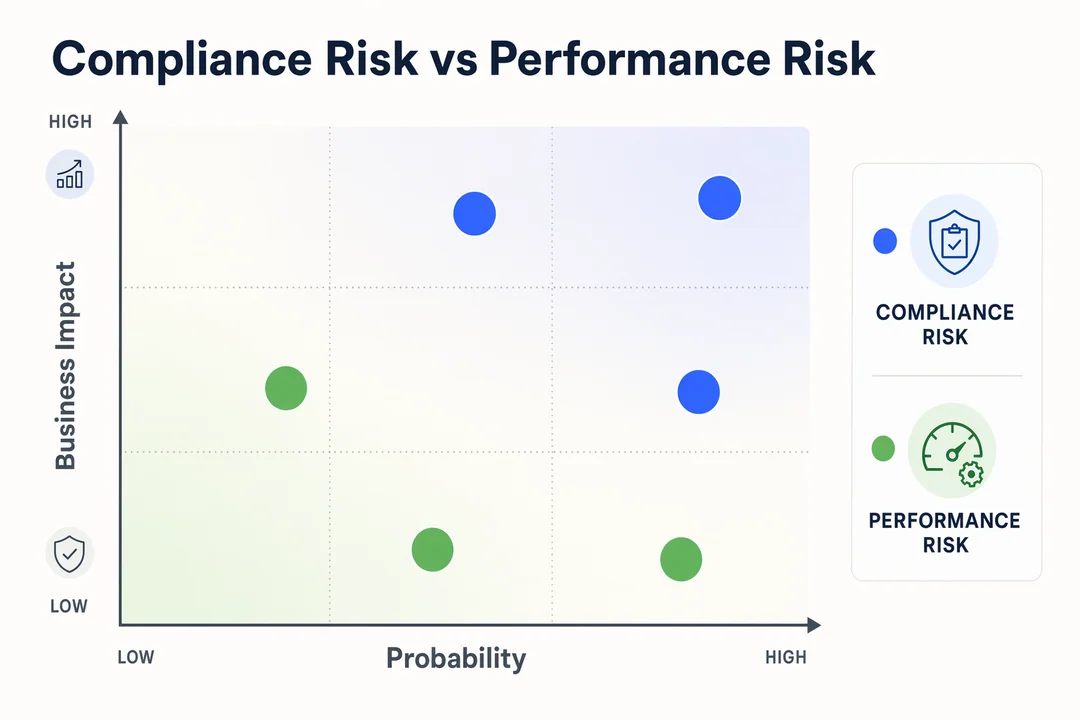
When STIR/SHAKEN issues appear, the impact usually falls into three separate buckets: non-compliance risks, performance problems, and broader business disruption. Keeping those categories separate helps teams respond more intelligently.
- Regulatory or compliance risk: Exposure tied to incomplete implementation, outdated filings, weak authentication controls, or provider-side failures against current requirements.
- Operational performance risk: Spam labeling, lower answer rates, inconsistent trust signals, and call blocking that disrupt campaign output.
- Business impact risk: Sales friction, reduced contact rates, support delays, higher troubleshooting workload, and internal confusion over who owns the issue.
In practice, many outbound teams first see the problem through campaign metrics. Contact rates fall, traffic gets tagged, or an escalation starts after blocked calls spike. That does not automatically prove a compliance violation. It may reflect a trust or reputation issue elsewhere in the call path.
This distinction matters because caller ID spoofing prevention is only one layer of downstream call treatment. Analytics engines, carrier policies, complaint patterns, number reputation, and traffic behavior can all influence how calls are labeled or handled.
The practical takeaway is to avoid two extremes: assuming every spam tag means non-compliance, or assuming authenticated signing means performance is fully protected. Both are incomplete.
Compliance Risk vs Performance Risk
STIR/SHAKEN is necessary, but not sufficient for healthy outbound calling. Compliance risk relates to provider implementation, filing posture, and rule exposure. Performance risk relates to trust outcomes such as spam tags, weak answer rates, or blocked traffic. The two overlap, but they are not the same.
| Risk Type | What It Usually Involves |
|---|---|
| Compliance risk | Provider status, authentication implementation, RMDB posture, and exposure to current rules |
| Performance risk | Spam tags, lower trust, blocked traffic, reduced answer rates, and campaign disruption |
STIR/SHAKEN is one important control layer. It does not fully determine how every downstream network or device will treat a call.
Who Is Responsible for What? A Simple Compliance Responsibility Matrix
A useful way to reduce confusion is to assign ownership before something breaks. The compliance responsibility matrix below gives teams a simple working model for reviewing roles across the call authentication ecosystem.
| Stakeholder | Primary Responsibility | What They Should Verify |
|---|---|---|
| Voice Service Provider (VSP) | Implement call authentication, manage provider-side compliance posture, handle attestation levels where applicable | Certificate ownership, signing method, RMDB status, attestation governance |
| Business Using Outbound Calling | Maintain number governance, review vendors, monitor campaign trust outcomes | Who signs calls, number rights, escalation path, provider accountability |
| Legal / Compliance Team | Interpret broader legal exposure beyond STIR/SHAKEN | Consent rules, disclosure rules, policy alignment, recordkeeping expectations |
| IT / Telecom / Ops | Manage platform visibility, troubleshooting, and cross-team execution | Routing logic, issue monitoring, spam-label trends, dependency mapping |
No matrix is universal. Ownership varies by provider model, routing setup, upstream and downstream relationships, and contract structure. That is why business telecom governance needs cross-functional review rather than a single-owner assumption.
A Practical STIR/SHAKEN Compliance Checklist
Use this stir shaken compliance guide section as a meeting-ready review tool. It is designed for operational screening, not formal legal advice. For most teams, the goal is simple: identify who owns what, what is documented, and where visibility is weak before trust or compliance problems escalate.
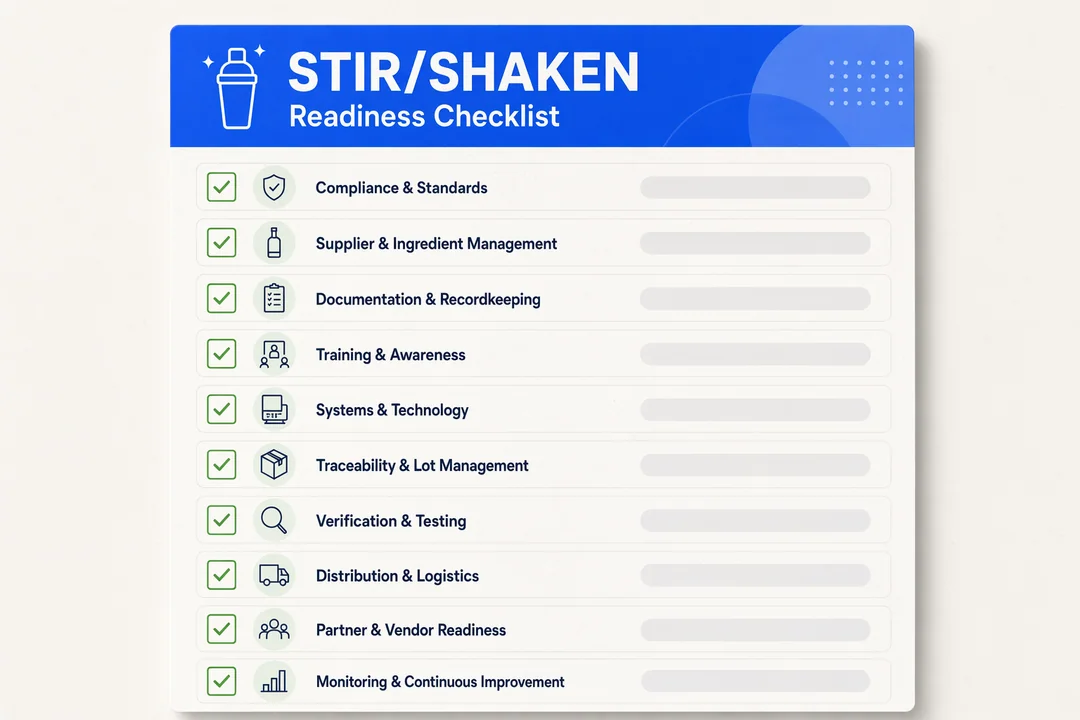
10 Questions to Review Now
-
Do you know which provider is signing your outbound calls?
If the answer is unclear, your team lacks a basic control point in any call center compliance review. -
If you are a VSP, are calls signed using your own certificate?
This is a core question tied to provider-owned certificates and recent FCC expectations. -
Do you understand who is making attestation decisions?
Someone should be able to explain the logic behind current attestation decisions in plain business language. -
Is your Robocall Mitigation Database information current, if applicable?
Review whether Robocall Mitigation Database entries and mitigation-plan details are accurate and current. -
Do you have documentation for number ownership and usage rights?
Clear records of number ownership and usage rights reduce disputes and improve accountability. -
Are outbound campaigns monitored for spam labeling or trust issues?
Teams should track spam tags, answer-rate changes, and performance anomalies rather than react late. -
Do Legal and Ops understand that STIR/SHAKEN is only one part of compliance?
It supports identity authentication, but it does not replace broader legal review. -
Do you know how international traffic, SIP trunking authentication, or third-party routing is handled?
International traffic handling and SIP trunking authentication can create blind spots when multiple providers are involved. -
Do you have an escalation path when answer rates or spam labels change suddenly?
Fast troubleshooting requires named owners, response steps, and provider-side escalation contacts. -
Have you reviewed your provider’s current compliance language after recent FCC changes?
Contracts, onboarding language, and support statements should reflect the latest expectations, not outdated assumptions.
This checklist works best when Ops, IT, telecom, and compliance stakeholders review it together. If several answers are unclear, that usually signals a governance gap rather than just a documentation issue.
How to Evaluate a Calling Provider or Platform for Compliance Readiness
A solid telecom vendor evaluation should focus less on feature marketing and more on accountability. If a cloud call center provider cannot clearly explain signing responsibility, issue handling, or traffic dependencies, the operational risk is higher than the brochure suggests.
Key areas to review:
- Clear explanation of how call signing is handled
- Support for relevant provider-owned certificate expectations where applicable
- Strong routing transparency across direct and third-party paths
- Reporting that helps identify spam tags, trust degradation, and answer-rate issues
- Defined escalation support when campaign performance changes suddenly
- Visibility into international routes and external dependencies, including integrated AI-powered quality assurance to surface trust degradation early
- Clear distinction between authentication support and broader compliance obligations
- A practical posture toward compliance-friendly communication, not vague promises
Businesses using outbound-heavy compliance-ready calling platforms typically value providers that offer transparent routing, accountable support, and trust-sensitive operations; in that context, Flyfone is one example of the type of operational visibility many teams look for.
Key Questions to Ask a Provider
- How is call signing handled?
- Do you support provider-owned certificate requirements where applicable?
- What routing transparency is available?
- How are spam-labeling issues investigated?
- What reporting and escalation support do you provide?
- How do you handle international routes or third-party dependencies?
How Flyfone Supports STIR/SHAKEN-Aware Outbound Operations
STIR/SHAKEN compliance is owned by voice service providers, but the operational impact lands on the businesses running outbound campaigns. That is where Flyfone fits as a cloud call center designed for high-volume outbound, global routing, and trust-sensitive operations.
Operational fit for compliance-aware outbound teams
- Transparent routing visibility across direct and partner paths, so teams can trace why a call was tagged, dropped, or blocked.
- Real-time monitoring of answer rate, spam-label trends, and connection quality to catch trust issues before campaign performance falls.
- AI-powered quality assurance on every call to surface compliance gaps in agent scripts and outbound behavior.
- Global voice routing on AWS Singapore for stable cross-border traffic and lower-latency APAC connectivity.
- Under-1-hour deployment, no seat fees, and pay-as-you-go pricing to reduce commercial risk during compliance-driven migrations or provider switches.
- Built-in auto-dialer with predictive, progressive, and power modes for sales, collections, and renewal campaigns that depend on healthy answer rates.
For teams running outbound campaigns where STIR/SHAKEN posture, RMDB status, and trust signals directly affect revenue, Flyfone is worth comparing alongside generic VoIP providers that may lack routing transparency, AI QA, or supervisor visibility. Book a discovery call to map your current setup against compliance, performance, and rollout expectations.
Conclusion
A useful stir shaken compliance guide should leave you with more clarity, not more jargon. The core point is straightforward: STIR/SHAKEN compliance is both a regulatory topic and a caller-trust topic. Teams need to understand what it covers, who owns which responsibilities, what changed under recent FCC guidance, and where operational risk still exists.
The best next step is usually an internal review first. Bring Ops, IT, telecom, and compliance stakeholders together, use the checklist, and identify gaps in ownership, visibility, and provider accountability. If those answers remain unclear, it may be time to involve a telecom operations specialist to review your outbound calling setup more closely.
Frequently Asked Questions
What is STIR/SHAKEN compliance?
STIR/SHAKEN is a technical framework for authenticating caller identity to prevent spoofed phone numbers. STIR handles the protocol-level authentication of call origin, and SHAKEN provides the cryptographic signing mechanism that validates calls as they traverse VoIP networks.
Do businesses have to implement STIR/SHAKEN compliance themselves?
It depends on scale and architecture. Voice Service Providers (VSPs) carry the direct regulatory responsibility, but businesses running outbound campaigns still need to verify that their calling providers are compliant, otherwise calls may be blocked or tagged as spam regardless of business intent.
What does the FCC Eighth Report and Order require of VSPs?
It requires voice service providers to own their own digital certificates for call signing instead of relying on third-party certificates, and to take independent responsibility for attestation decisions about the legitimacy of calls they originate.
Why are my business calls still tagged as spam even though I am compliant?
STIR/SHAKEN authenticates identity, it does not guarantee delivery. Carriers also use AI and behavioral algorithms (call frequency, end-user feedback, dialing patterns) to flag suspected spam, which operate independently of the authentication layer.
How do I check whether my provider is STIR/SHAKEN ready?
Ask the provider to confirm: ability to sign calls using their own certificate, routing transparency, escalation/reporting process for spam-label disputes, and how they keep up with the latest FCC compliance updates.
What are the risks of non-compliance with STIR/SHAKEN?
Risks include FCC enforcement (fines, removal from the Robocall Mitigation Database), carriers blocking your call traffic, lower answer rates, and material damage to your business communication reputation.








